Some Apple users are секс с женой помешал ребенок порнографиейreportedly being targeted by a sophisticated attack, requesting them to hand over their Apple ID credentials over and over again.
According to KrebsonSecurity, the attack starts with unsuspecting Apple device owners getting dozens of system-level messages, prompting them to reset their Apple ID password. If that fails, a person pretending to be an Apple employee will call the victim and try to convince them into handing over their password.
SEE ALSO: Apple confirms dates for WWDC 2024This is exactly what happened to entrepreneur Parth Patel, who described their experience on Twitter/X. First, all of Patel's Apple devices, including their iPhone, Watch, and MacBook, started displaying the "Reset Password" notifications. After Patel clicked "Don't Allow" to more than one hundred requests, the fake Apple Support called, spoofing the caller ID of Apple's official Apple Support line. The fraudster Apple employee actually knew a lot of Patel's real data, including email, address, and phone number, but they got their name wrong, which had confirmed Patel's suspicions that they were under attack.
This Tweet is currently unavailable. It might be loading or has been removed.
While the attack was ultimately unsuccessful in this example, it's easy to imagine it working. The victim might accidentally allow the password reset (mistakes are easy to happen when you have to click on something hundreds of times), or they could fall for the fairly convincing, fake Apple Support call.
Patel's example isn't isolated, either; KrebsonSecurity has details on a very similar attack that happened to a crypto hedge fund owner identified by his first name, Chris, as well as a security researcher identified as Ken. In Chris' example, the attack persisted for several days, and also ended with a fake Apple Support call.
How did the attackers know all the data needed to perform the attack, and how did they manage to send system-level alerts to the victims' phones? According to KrebsonSecurity, the hackers likely had to get a hold of the victim's email address and phone number, associated with their Apple ID. Then they used an Apple ID password reset form, that requires an email or phone number, alongside a CAPTCHA, to send the system-level, password reset prompts. They also likely used a website called PeopleDataLabs to get information on both the victim and Apple employees they impersonated.
But there could also be a bug in Apple's systems, which should in theory be designed not to allow someone to abuse the password reset form and send dozens of requests in a short period of time (Apple did not respond to KrebsonSecurity's request for comment).
It appears that there's no easy or foolproof way to protect oneself from such an attack at this time, save from changing one's Apple ID credentials and tying them to a new number and email. It's hard to tell how widespread this attack is, but Apple users should be vigilant and triple-check the authenticity of any password reset request, even if it appears to come from Apple itself.
For on spammers and scammers, check out Mashable's series Scammed, where we help you navigate a connected world that’s out for your money, your information, or just your attention.
Topics Apple Cybersecurity
Previous:The Shogun of Santas
 June Kuramoto and Friends to Present 'Concert Under the Stars'
June Kuramoto and Friends to Present 'Concert Under the Stars'
 Amazon Big Spring Sale: Loftie smart alarm clock deal
Amazon Big Spring Sale: Loftie smart alarm clock deal
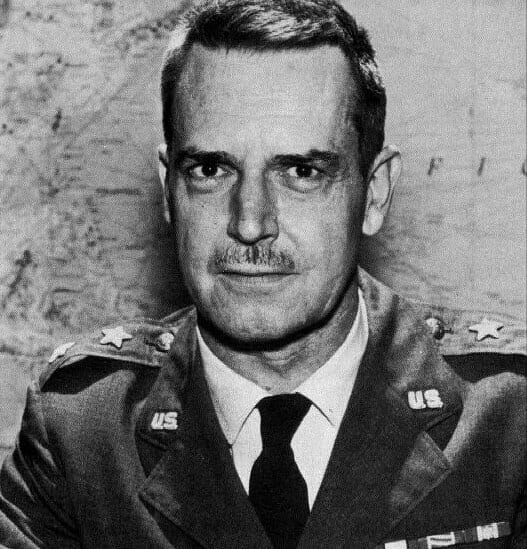 Max Boot’s Vietnam
Max Boot’s Vietnam
 Tribute to a Dancer
Tribute to a Dancer
 'The White Lotus' Season 3, episode 7 reveals who robbed the hotel
'The White Lotus' Season 3, episode 7 reveals who robbed the hotel
 Amazon Big Spring Sale 2025: Save $170 on Dyson Hot+Cool
Amazon Big Spring Sale 2025: Save $170 on Dyson Hot+Cool
 Best water bottle deal from Amazon's Big Spring Sale
Best water bottle deal from Amazon's Big Spring Sale
 Sharing His 'Heroic Idealism'
Sharing His 'Heroic Idealism'
 Best earbud deal: Save $30 on Anker Soundcore Sleep A20 earbuds
Best earbud deal: Save $30 on Anker Soundcore Sleep A20 earbuds
 Learning from a Koto Legend at Nishi Center in Little Tokyo
Learning from a Koto Legend at Nishi Center in Little Tokyo
 Kitchen-Sink Drama
Kitchen-Sink Drama
 The Midterms and the Turn Leftward
The Midterms and the Turn Leftward
 Amazon Spring Sale 2025: Best Bang & Olufsen H95 headphones deal
Amazon Spring Sale 2025: Best Bang & Olufsen H95 headphones deal
 Celebration of Life for Bob Suzuki at Cal Poly Pomona
Celebration of Life for Bob Suzuki at Cal Poly Pomona
 Today's Hurdle hints and answers for March 30, 2025
Today's Hurdle hints and answers for March 30, 2025
 Wordle today: The answer and hints for March 31, 2025
Wordle today: The answer and hints for March 31, 2025
 In Praise of Negative Reviews
In Praise of Negative Reviews
 Ondo at Music Center Plaza
Ondo at Music Center Plaza
 Amazon Spring Sale 2025: Best Kindle Scribe deal
Amazon Spring Sale 2025: Best Kindle Scribe deal
There's a great new Michael Jordan meme thanks to 'The Last Dance'The best sports animeGive poor people a guaranteed income and let them spend it however they pleaseGina Martin on the power of activism and how she made upskirting illegalWhy the Arctic's unprecedented ozone hole fizzed out'Disney Gallery: The Mandalorian' Ep 1 has a great Dave Filoni story'Disney Gallery: The Mandalorian' Ep 1 has a great Dave Filoni storyElon Musk's latest misinformation tweets are about protecting TeslaStreaming films are eligible for next year's Academy Awards — but there's a catchPrivacy experts reviewed popular video Warzone left “unplayable” after botched Season 3 Reloaded update Best Warzone SMG loadouts in Season 3 Reloaded Black Ops 6 players convinced battle pass XP has been secretly nerfed Chol Soo Lee’s Story Told in New Documentary Black Ops 6 & Warzone Got Your Six event start date & rewards EWP’s Vision Awards to Honor Kristina Wong, Randall Tamura Warzone cheaters can now completely avoid bans despite being caught Best guns in Warzone Season 4 All Warzone bunker codes: Locations, map, more Japanese Emperor, Empress to Attend Queen’s Funeral
0.1743s , 8006.0390625 kb
Copyright © 2025 Powered by 【секс с женой помешал ребенок порнографией】Apple users targeted by annoying 'Reset Password' attack,Feature Flash